Queen Mary University of London Job Site "Hacked"
At the weekend I was sent a link by a colleague to the jobs' site of Queen Mary University (job site here) as they wanted my advice on a position. I recommended the position but suggested using an alternative method of submitting an application, the site really does not utilise standard security practises (e.g. mixed content over HTTPS, account enumeration, password policy etc).
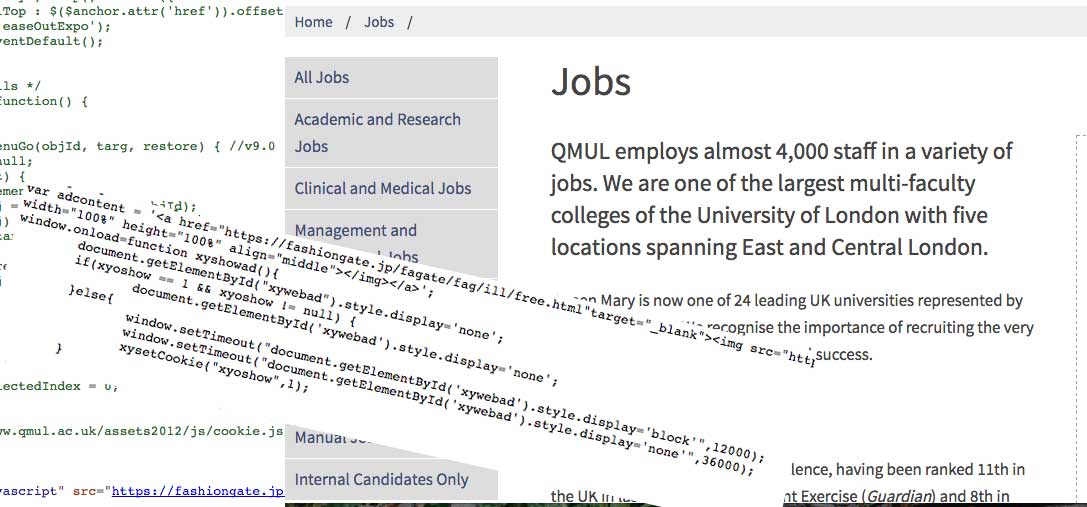
Nothing surprised me about the website, until I tried to click on a URL located within the job listing, it automatically directed me to the following:

The first thought that went through my mind was "oh boy, have I got malware on my machine?!", I went back to the listing and tried clicking the link, it again redirected me to a new advert. I was confident that it was not an issue with my laptop, or any malware loaded on my machine.
What may have happened
Queen Mary have not provided any details of the incident, as is common, however it has all the hallmarks of a cross-site scripting attack. That is, a malicious third party has introduced client-side scripts into webpages viewed by other users.
I will admit I am speculating but these types of incidents usually point towards something more serious, such as a compromised database or server system.
What is the hack?
For those who are interested in what I am labelling 'the hack', read on!
I decided to take a look at the source code of the Queen Mary jobs' site, the following had been injected into the code after the